Database
Database SQL Injection Attacks

SQL injection attacks are one of the oldest and most well-known security threats facing database-driven applications, yet they remain a persistent and serious risk. Despite years of awareness and improvements in frameworks and tools, SQL injection continues to be responsible for data breaches, unauthorized access, and system compromise across many industries. Understanding how these attacks work and how to avoid them is essential for anyone involved in designing, developing, or maintaining systems that interact with databases.
At a basic level, a SQL injection attack occurs when an attacker is able to manipulate an application’s database query by inserting malicious SQL code into user input. Many applications accept input from users through forms, URLs, cookies, or APIs and then use that input to build SQL statements. If the application does not properly handle this input, an attacker can alter the structure of the query itself. Instead of the database executing only the intended command, it may execute additional or modified commands supplied by the attacker.
The root cause of SQL injection vulnerabilities lies in the way SQL queries are constructed. In insecure applications, user input is often concatenated directly into SQL strings. For example, an application might build a query by inserting a username and password directly into a SELECT statement. If an attacker enters carefully crafted input that includes SQL syntax, the database may interpret it as part of the command rather than as plain data. This can allow the attacker to bypass authentication, retrieve sensitive data, modify records, or even execute administrative operations.
SQL injection attacks can take many forms. One common type is authentication bypass, where an attacker manipulates a login query so that it always evaluates as true. By inserting conditions such as logical operators, the attacker can trick the database into granting access without valid credentials. Another form is data extraction, where attackers use injection techniques to retrieve entire tables of information, including usernames, passwords, credit card numbers, or personal data.
More advanced attacks involve blind SQL injection, where the attacker does not receive direct error messages or query results. Instead, they infer information by observing differences in application behavior, such as response times or error messages. Time-based blind SQL injection, for example, uses database functions that cause delays when certain conditions are true. By measuring response times, attackers can gradually extract data bit by bit. These attacks demonstrate that simply hiding error messages is not enough to prevent exploitation.
The impact of a successful SQL injection attack can be severe. Attackers may gain unauthorized access to sensitive data, leading to privacy violations and regulatory penalties. They may alter or delete data, disrupting business operations or corrupting critical records. In some cases, attackers can escalate their access to the underlying operating system, potentially taking control of the server hosting the database. The financial, legal, and reputational damage from such incidents can be significant and long-lasting.
Avoiding SQL injection attacks starts with secure coding practices. The single most effective defense is the use of parameterized queries, also known as prepared statements. In this approach, the SQL query is defined with placeholders for user input, and the input values are bound to those placeholders separately. This ensures that the database treats user input strictly as data, not as executable SQL code. Even if an attacker includes SQL syntax in their input, it will not change the structure of the query.
Stored procedures can also help reduce the risk of SQL injection when used correctly. When stored procedures accept parameters and avoid dynamic SQL, they provide a layer of abstraction between user input and database operations. However, it is important to note that stored procedures are not automatically safe. If they build dynamic SQL internally using unvalidated input, they can still be vulnerable. The key principle remains the same: separate code from data.
Input validation is another important defensive measure, although it should not be relied upon alone. Validating input involves checking that user-supplied data conforms to expected formats, lengths, and character sets. For example, numeric fields should only accept numbers, and text fields should have reasonable length limits. While validation can reduce the attack surface and prevent some malformed input, it is not sufficient by itself. Skilled attackers can often bypass validation rules, so validation should be combined with other protections.
Escaping user input is sometimes used as a defense, but it is generally less reliable than parameterized queries. Escaping attempts to neutralize special characters by adding escape sequences so they are treated as literal values. This approach is error-prone because escaping rules vary between database systems and contexts. Mistakes or inconsistencies can leave gaps that attackers exploit. For this reason, escaping should be considered a secondary measure rather than a primary defense.
Principle of least privilege plays a crucial role in limiting the damage of SQL injection attacks. Applications should connect to databases using accounts with only the permissions they absolutely need. For example, an application that only reads data should not have permission to modify or delete records. If an attacker manages to exploit a SQL injection vulnerability, limited privileges can significantly reduce what they are able to do. This containment strategy does not prevent the attack, but it can mitigate its impact.
Error handling and messaging also influence SQL injection risk. Detailed database error messages can provide attackers with valuable information about database structure, table names, and query syntax. Applications should avoid exposing raw database errors to users. Instead, they should log detailed errors internally while presenting generic messages to users. This reduces the information available to attackers without sacrificing the ability to troubleshoot issues.
Regular security testing is an essential part of preventing SQL injection vulnerabilities. Code reviews, automated static analysis, and dynamic testing tools can help identify insecure query construction before it reaches production. Penetration testing and vulnerability scanning can reveal weaknesses in deployed systems. Because applications evolve over time, testing should be ongoing rather than a one-time activity. New features and changes can introduce vulnerabilities even in previously secure systems.
Database configuration and hardening also contribute to defense against SQL injection. Disabling unnecessary features, applying security patches promptly, and configuring logging and monitoring can help detect and respond to suspicious activity. Intrusion detection systems and database firewalls can sometimes identify patterns associated with injection attacks and block them in real time. While these measures should not replace secure coding practices, they add additional layers of protection.
Education and awareness are often overlooked but are vital to long-term security. Developers, database administrators, and system architects need to understand how SQL injection works and why certain practices are dangerous. Many vulnerabilities arise not from malice but from lack of knowledge or time pressure. Establishing secure coding standards and providing regular training helps create a culture where security is considered a fundamental requirement rather than an afterthought.
It is also important to recognize that SQL injection is not limited to traditional web applications. APIs, mobile apps, background jobs, and administrative tools can all be vulnerable if they construct SQL queries using untrusted input. Any interface that accepts external data and interacts with a database should be designed with the same level of caution. Attackers often target less obvious entry points that receive less scrutiny.
Ultimately, preventing SQL injection attacks requires a layered approach. No single technique is sufficient on its own. Parameterized queries form the foundation, supported by input validation, least privilege, careful error handling, regular testing, and strong operational practices. When these measures work together, they significantly reduce both the likelihood and impact of SQL injection attacks.
Despite being a well-understood threat, SQL injection remains relevant because it exploits fundamental mistakes in how applications interact with databases. By treating user input with appropriate skepticism and designing systems that clearly separate code from data, organizations can protect their databases and the valuable information they contain. In an era where data breaches can have far-reaching consequences, taking SQL injection seriously is not optional but essential for responsible system design.
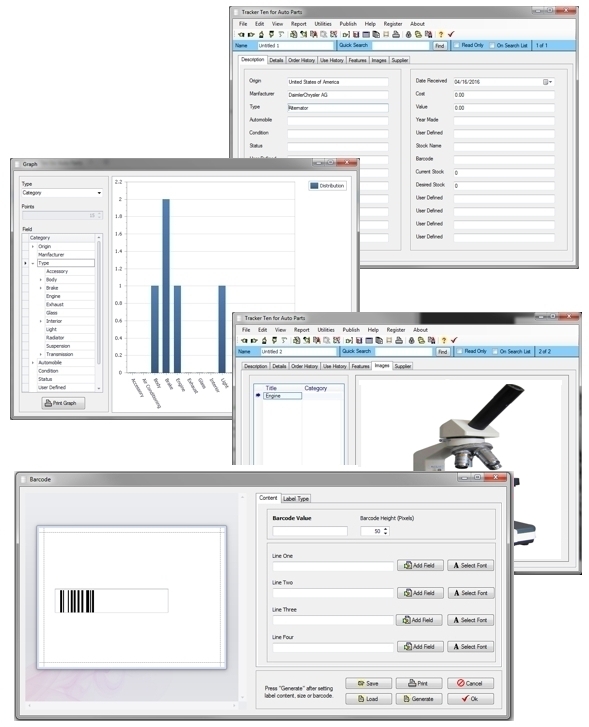
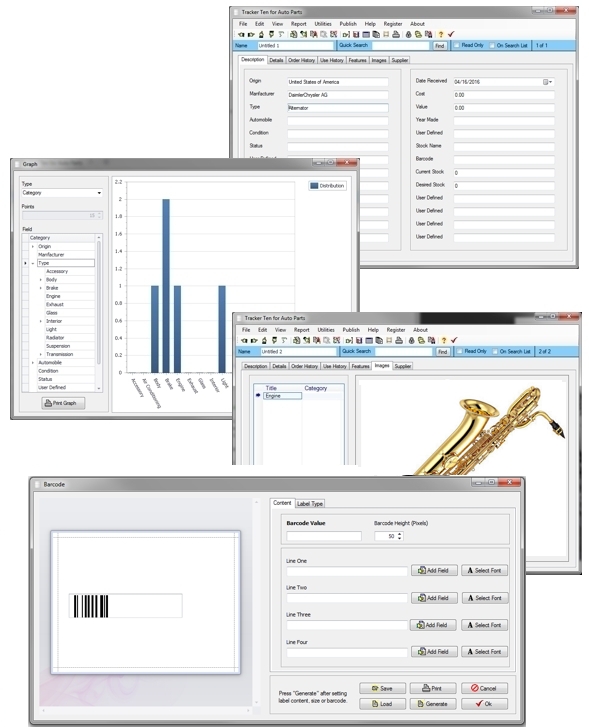
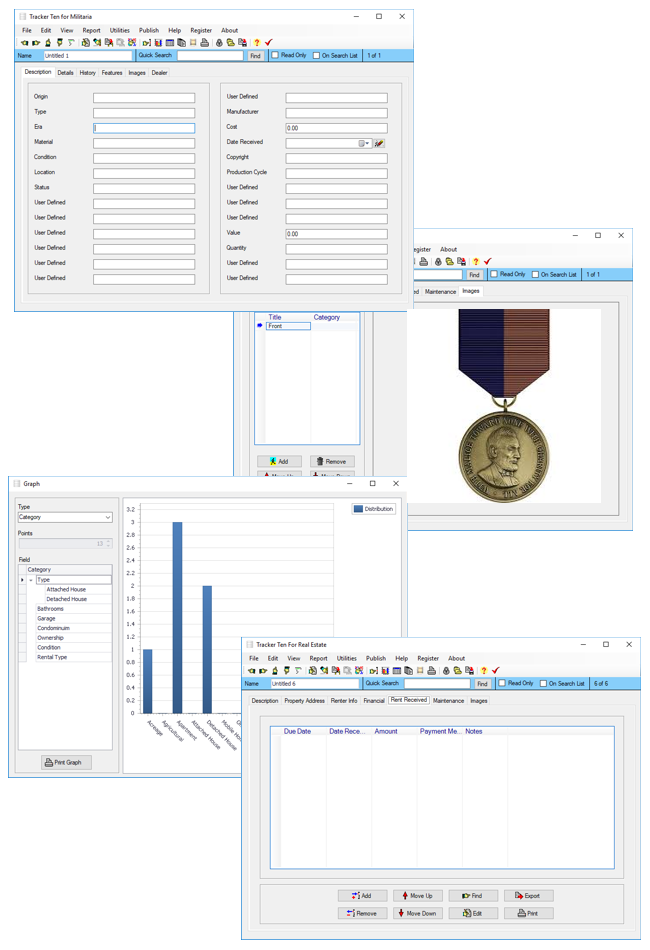
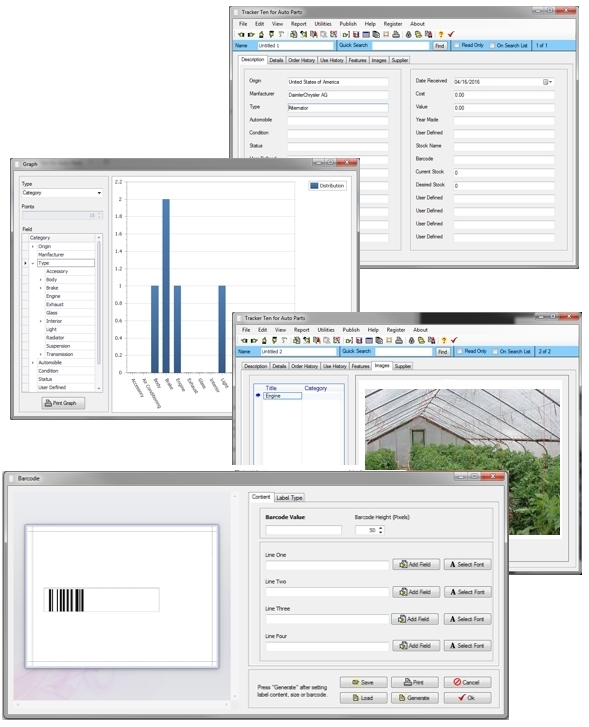
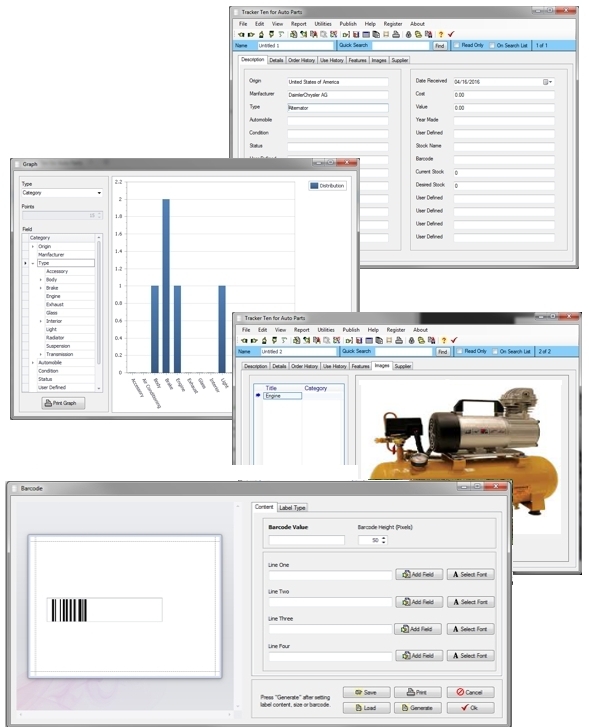
Looking for windows database software? Try Tracker Ten
- PREVIOUS Database User Interface Tuesday, December 19, 2023
- NextWhat To Consider When Choosing A Reliable Shipping Company Thursday, December 14, 2023